When you connect to a VPN, your computer creates an encrypted “tunnel” between itself and the VPN server. This tunnel prevents anyone on your local network from intercepting your data and keeps your web activity private.
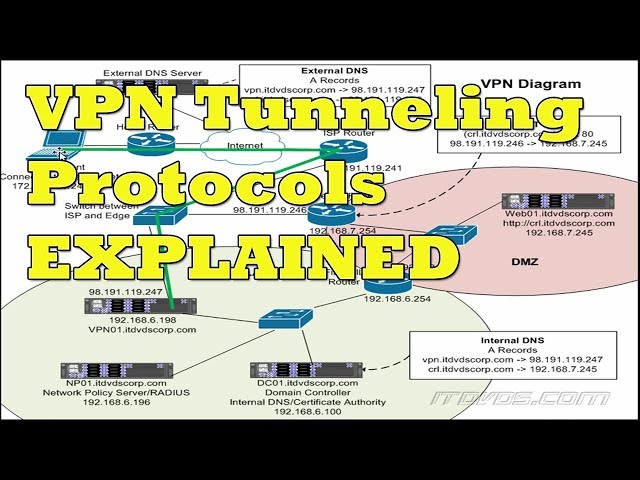 Checkout this video:
Checkout this video:
Introduction
A VPN, or Virtual Private Network, is a network that allows for secure and private connections over the internet. This can be accomplished through the use of encryption and other security measures. One of the most important aspects of a VPN is ‘tunneling’.
Tunneling is the process of encapsulating data so that it can be securely sent over a network. This is often done with the help of a tunneling protocol. A tunneling protocol will create a ‘tunnel’ between two devices in order to send data. This tunnel will be encrypted in order to keep the data safe from eavesdroppers.
There are many different tunneling protocols that can be used in order to create a VPN. Some of the most popular protocols include PPTP, L2TP/IPSec, and OpenVPN. Each of these protocols has its own advantages and disadvantages.
PPTP is one of the oldest tunneling protocols and is very easy to set up. However, it is not as secure as some of the other options and has been known to be vulnerable to attack.
L2TP/IPSec is a more secure option than PPTP but can be more difficult to set up. It uses two layers of security, which makes it more difficult for attackers to penetrate.
OpenVPN is an open-source protocol that offers a high level of security. It is also relatively easy to set up compared to some of the other options.
Choosing the right tunneling protocol for your VPN will depend on your needs and preferences. If you are looking for a high level of security, then OpenVPN might be the best option for you. However, if you need something that is quick and easy to set up, then PPTP might be a better choice.
What is a VPN?
A VPN, or Virtual Private Network, is a private network that extends across a public network or the Internet. A VPN lets its users “tunnel” through the public network to send and receive data privately.
A VPN is created by establishing a virtual point-to-point connection through the use of dedicated connections, virtual tunneling protocols, or traffic encryption. A VPN available from the public Internet can provide some of the benefits of a wide area network (WAN). From a user perspective, the resources available within the private network can be accessed remotely.
VPNs can be used to secure private communications between an organization’s employees and remote workers. They can also be used to connect an organization’s internal network with its remote offices or cloud computing resources.
What is Tunneling?
Tunneling is the process of taking a data packet and encapsulating it in another data packet so it can be transmitted across a network. The encapsulation process adds a layer of headers and trailers to the original data packet to create the new data packet. The source and destination addresses in the new data packet are set to the tunneling server’s address. When the tunneling server receives the new data packet, it decapsulates it, removes the headers and trailers, and sends the original data packet to its intended destination.
There are two types of tunneling: volumetric tunneling and datagram tunneling. Volumetric tunneling allows an entire network connection to be carried within another connection. Datagram tunneling only allows individual data packets to be encapsulated and transported.
Tunneling is used in a VPN to encrypt all traffic passing through the VPN. This ensures that any eavesdroppers on the network will not be able to read or modify the traffic. Tunneling also allows a VPN to bypass firewall restrictions by encapsulating all traffic in a format that is allowed by the firewall.
How is Tunneling Accomplished in a VPN?
A VPN tunnel is created when a connection is made between two endpoints. The first endpoint is known as the VPN client, while the second endpoint is known as the VPN server. In order to create a secure connection, the data that is being sent between these two endpoints must be encrypted. This process is known as tunneling.
Tunneling works by encapsulating the data that is being sent into a packet. This packet is then sent through the tunnel, which is a secure connection between the two endpoints. Once the packet reaches the other side of the tunnel, it is decrypted and the data is then able to be used.
Tunneling is a great way to keep data secure, as it makes it very difficult for anyone to eavesdrop on the traffic that is passing through the tunnel. Additionally, tunneling can also be used to bypass firewalls and other security measures that may be in place.
Conclusion
In conclusion, we have seen that tunneling is a powerful tool that can be used to improve your VPN experience. By creating a secure tunnel between your device and the VPN server, you can ensure that all of your data is protected from prying eyes. In addition, tunneling can also be used to bypass restrictions and access blocked websites.
